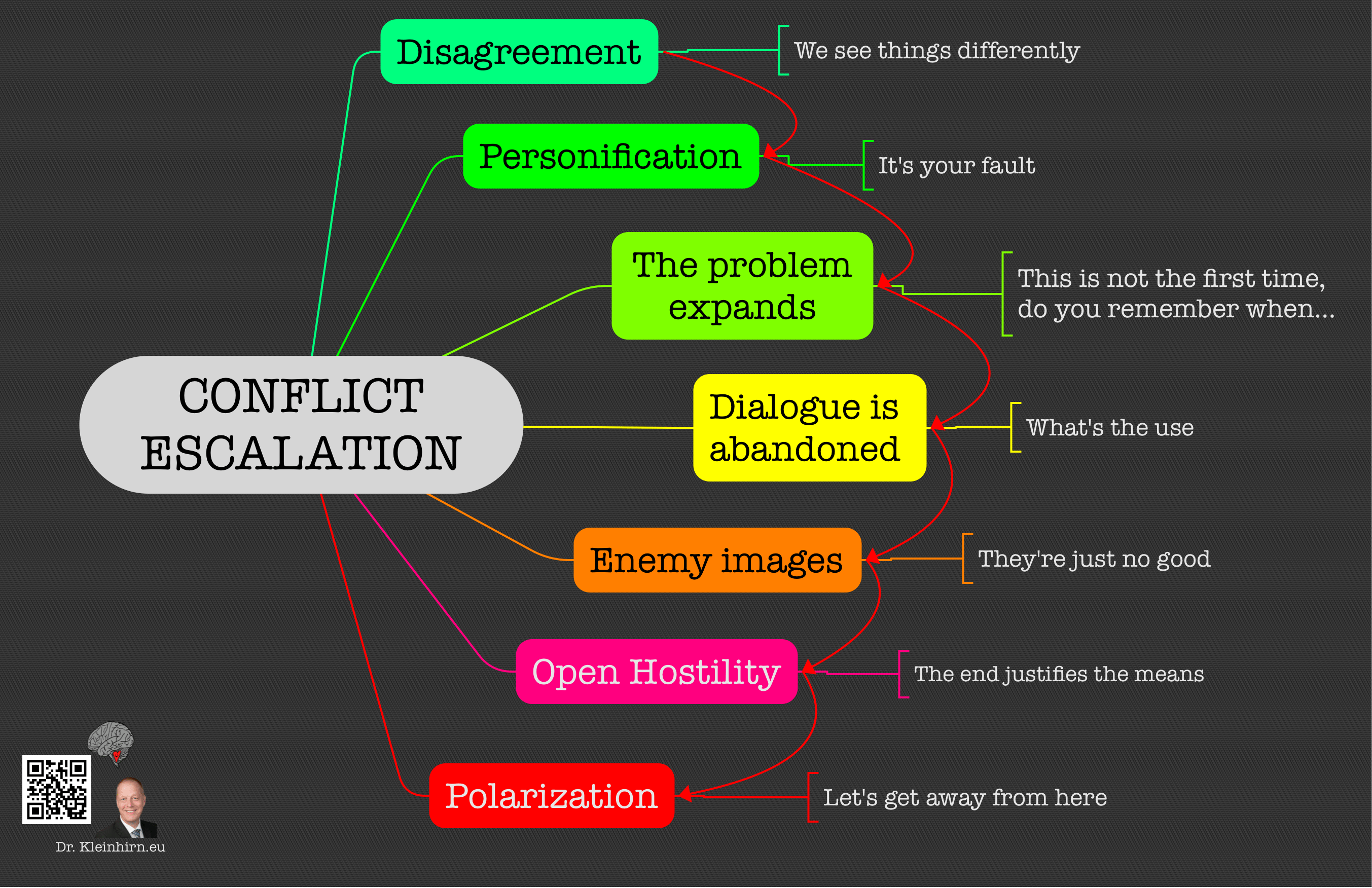
The transition from shadow warfare to explicit threats of decapitation against heads of state marks a fundamental shift in the deterrence calculus of West Asia. When Iranian officials verbalize the intent to "pursue and kill" a sitting Prime Minister, they are not merely engaging in rhetoric; they are signaling a move from tactical containment to an existential attrition model. This escalation is driven by a breakdown in the traditional "gray zone" rules of engagement, where plausible deniability once provided a safety valve against total war. Understanding this shift requires an analysis of the structural incentives, the technical capabilities of non-state proxies, and the psychological operations surrounding high-value target (HVT) survival.
The Architecture of Threat Credibility
The credibility of a threat to a head of state relies on three distinct operational pillars. Without the alignment of these variables, such statements remain localized political theater.
- Intelligence Penetration: The ability to track HVT movements in real-time. This involves signals intelligence (SIGINT) and human intelligence (HUMINT) networks capable of bypassing the most sophisticated "ring of steel" security protocols in the world.
- Delivery Mechanisms: The availability of precision-guided munitions (PGMs), loitering munitions, or kinetic strike teams within operational range of the target.
- Political Will to Breach Redlines: The calculation that the retaliatory cost of an assassination—likely a full-scale regional war—is lower than the perceived benefit of removing the leadership figure.
The current Iranian posture suggests a recalculation of the third pillar. By publicizing the intent to target Benjamin Netanyahu, Tehran seeks to create a "permanent state of siege" within the Israeli security cabinet. This is a form of cognitive warfare designed to force the allocation of massive defensive resources, thereby thinning out protection for lower-tier strategic assets.
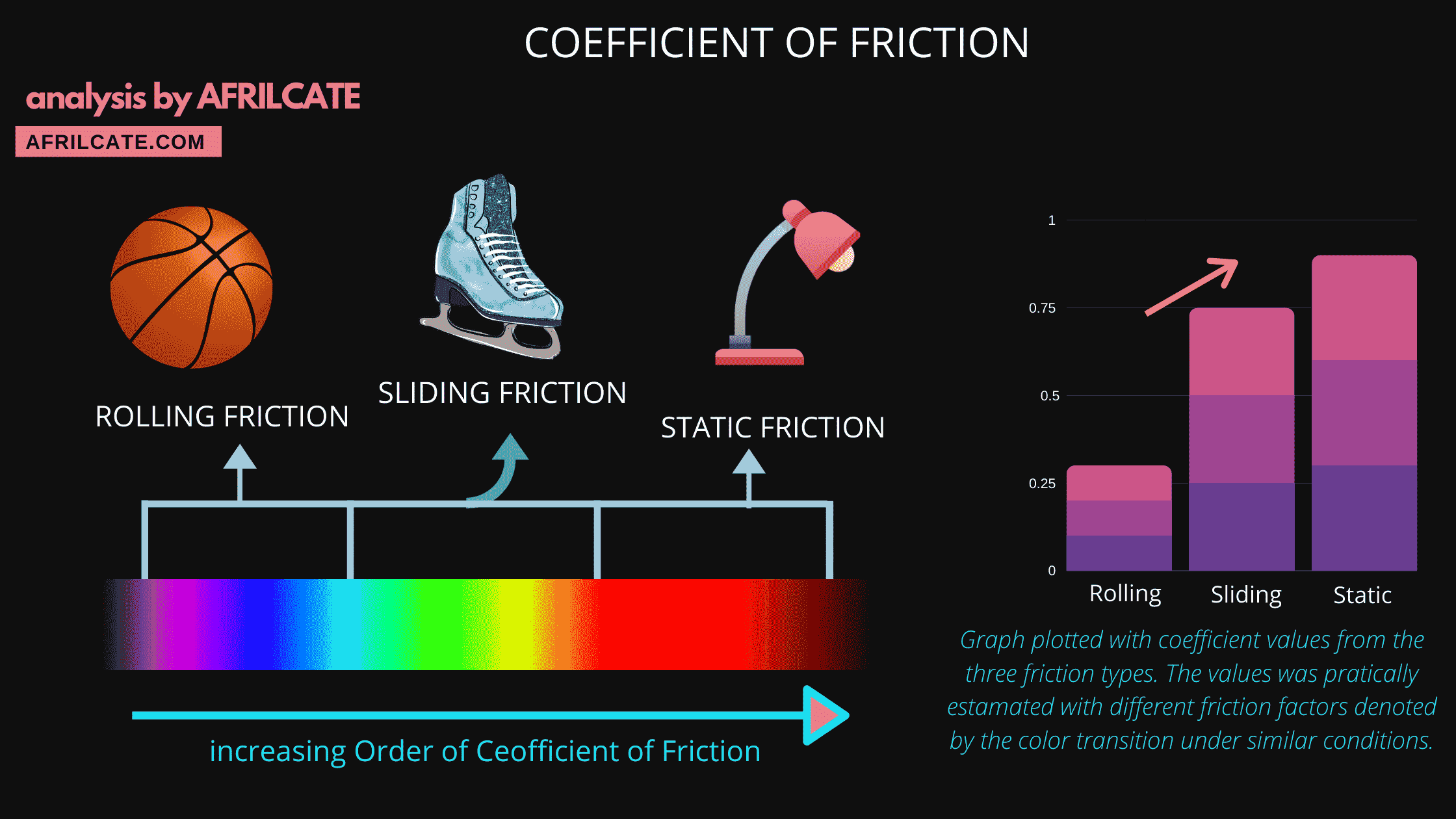
Asymmetric Attrition and the Cost of Defense
Israel’s defense strategy is predicated on a technological edge, specifically the multi-layered missile defense system comprising Iron Dome, David’s Sling, and Arrow-3. However, the cost function of this defense is inherently unfavorable when facing sustained asymmetric threats.
The economic equation of this conflict can be modeled as:
$$C_{total} = (N_{a} \times C_{i}) + D_{s}$$
Where:
- $N_{a}$ is the number of incoming low-cost assets (drones/rockets).
- $C_{i}$ is the cost of the interceptor (often 10x to 100x the cost of the threat).
- $D_{s}$ is the systemic economic disruption caused by alerts and psychological stress.
When Iran or its proxies target a specific individual, they force the defender to maintain a $100%$ interception rate. In a standard saturation attack, a $90%$ success rate is considered a victory. In a decapitation strike scenario, a $99%$ success rate is a failure. This binary outcome requirement places an immense structural strain on Israeli intelligence (Mossad and Shin Bet) and the Unit 730 protection detail.
The Information Vacuum and Rumor Weaponization
The "death rumors" surrounding high-ranking officials serve as a diagnostic tool for intelligence agencies. When rumors of a leader’s demise or incapacitation circulate, the subsequent communication patterns of the state provide a wealth of data for the adversary.
- Latency Analysis: How long does it take for the state to produce "proof of life"?
- Signature Verification: Are the videos or photos authenticated, or are they recycled or AI-generated?
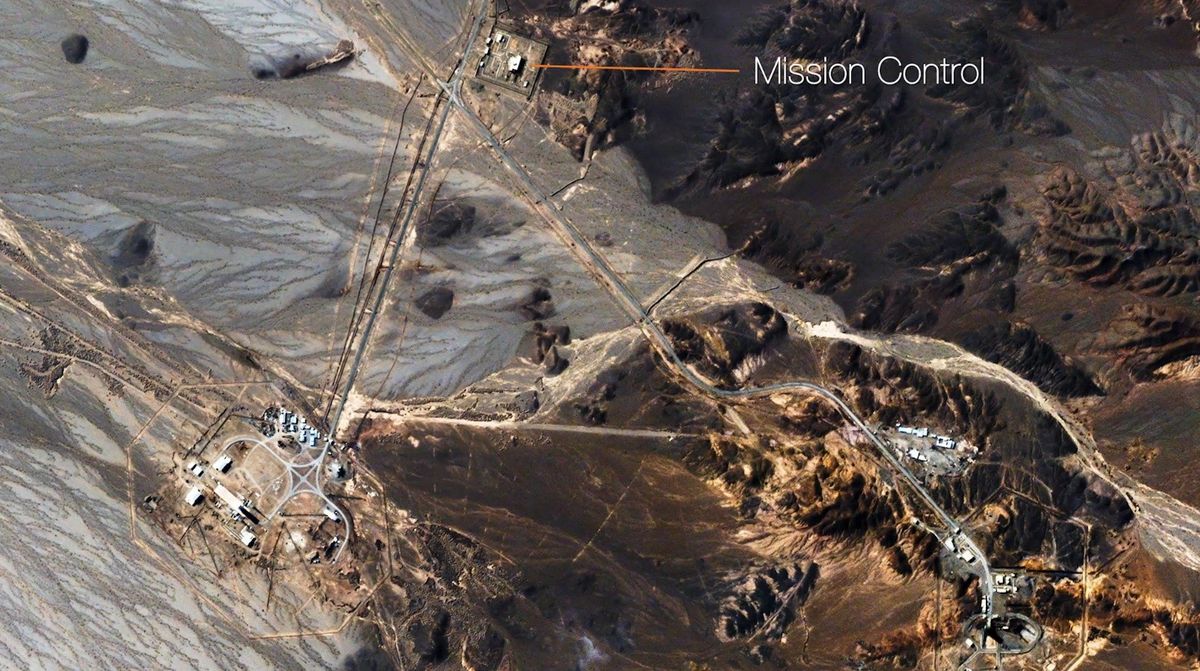
- Security Posture Shifts: Do satellite images show increased activity at medical facilities or command bunkers?
By threatening to "pursue and kill" a leader during a period of uncertainty, Iran leverages the information vacuum to destabilize public confidence. This is a deliberate application of Reflexive Control Theory—a Soviet-era technique where one side provides information tailored to lead the opponent to make a specific, predetermined decision.
Precision Strike Evolution and the 3D Threat Profile
The technical nature of the threat has evolved from crude rockets to multi-vector precision strikes. The modern assassination threat is no longer limited to a "lone wolf" or a sniper; it involves the synchronized use of:
- Loitering Munitions: Small, low-RCS (Radar Cross Section) drones that can hover near a target zone for hours before striking. Their ability to fly "under the radar" makes them particularly effective against specific residences or temporary outdoor venues.
- Cyber-Physical Attacks: Compromising the IoT (Internet of Things) or building management systems of a secure facility to disable exits, manipulate climate control, or provide real-time audio-visual feeds to attackers.
- Electronic Warfare (EW): Jamming the GPS and communication links of the protective detail, creating a "blackout" window during an extraction.
The strike on Netanyahu's private residence in Caesarea earlier in the conflict cycle demonstrated the vulnerability of static, well-known locations to UAV (Unmanned Aerial Vehicle) technology. This event forced a shift in Israeli leadership protocols, moving meetings to reinforced underground "pit" locations. This physical displacement is a tactical win for Iran, as it limits the leader's mobility and visibility, effectively achieving a "soft" neutralization of their public presence.
The Proxy Feedback Loop
Iran’s "Axis of Resistance" functions as a decentralized execution network. This creates a "many-to-one" threat profile that is difficult to neutralize through traditional state-to-state diplomacy.
- Hezbollah (North): Provides high-volume saturation to distract air defenses.
- Houthis (South): Introduce long-range PGM threats that require 360-degree monitoring.
- Iraqi/Syrian Militias (East): Act as launch pads for shorter-range, high-speed ballistic threats.
This network allows Tehran to maintain "strategic patience"—a term used to describe the willingness to wait for a lapse in security—while the proxies maintain constant, low-level pressure. The threat against the Israeli PM serves as the ideological glue for this coalition, framing the conflict not as a war against a state, but as a hunt for a specific "enemy of the revolution."
Strategic Implications of Decapitation Rhetoric
When a state actor officially adopts the language of assassination, it signals the abandonment of the "Westphalian" model of conflict, where leadership figures are generally considered off-limits to prevent total systemic collapse. This shift leads to several structural changes in regional dynamics:
- The End of Negotiated De-escalation: If one side believes the other is actively trying to kill its leader, the room for diplomatic backchannels shrinks to zero.
- Pre-emptive Escalation: The target state may feel compelled to launch a "decapitation strike" of its own to remove the threat at its source, leading to a vertical escalation ladder that terminates in direct state-on-state kinetic engagement.
- Shadow Mobilization: Security details become paramilitarized units, and the distinction between a leader’s "personal" and "state" life vanishes, further centralizing power within the security apparatus.
The "pursue and kill" doctrine is a high-risk gamble. While it achieves short-term psychological disruption, it creates a rigid environment where the only logical response from the opponent is a devastating counter-strike. The utility of the threat is currently being maximized as a deterrent against further Israeli strikes on Iranian soil, but its shelf life is limited. Once the threat is made, the failure to execute it diminishes the credibility of the speaker, while the successful execution of it almost certainly triggers a regional catastrophe.
The operational focus must now shift toward hardened redundancy. For the Israeli security state, this means moving beyond physical protection and into the realm of "distributed leadership" architectures, ensuring that the removal of a single individual does not result in the paralysis of the Command and Control (C2) system. For Iran, the challenge remains the gap between the rhetoric of "pursue and kill" and the technical reality of penetrating the world's most sophisticated counter-assassination environment. The friction between these two realities will dictate the next phase of the West Asia conflict.
The strategic play is to monitor the movement of high-level Iranian military commanders. If Tehran moves its own "hunting" units (such as specific Quds Force cells) into closer proximity to Israeli borders, the rhetoric has transitioned into an active operational phase. Until then, the primary theater remains the cognitive space, where the threat of the strike is intended to be more damaging than the strike itself.